Task Automation Introduces CyberRisk
Automated workflows are at the heart of many of the latest cloud software services we’ve seen emerge over the past few years…
Cyber Crime and When to Call the Cops
A compromised network requires a fast response. Understandably, your immediate actions will focus on removal of the threat and restoring normal operations. You may have met your SLA, but did you know that you’re missing…
Moving from the Top 4 to the Essential Eight
The Australian Cyber Security Centre’s (ACSC) threat report, released late last year, highlighted the evolution of cyber threats across…
McAfee Focus ’16 – Our talk: "From Zero to MSS in 0.3 seconds"
The McAfee event is one of the biggest security events in the world, bringing together more than 3,500 security experts…
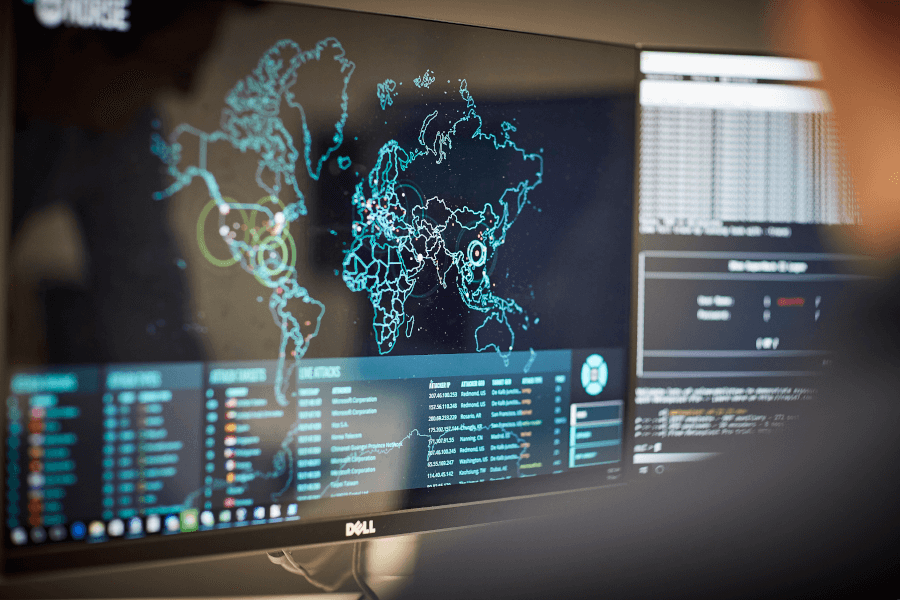
What we can learn from the ABC’s Four Corners program on Cyber War

The ABC’s recent Four Corners program is a must-see for anyone using technology today. This well-researched and easily consumable…